Zero Trust Cloud Security 2026: India’s Ultimate Defense Against AI-Powered Cyber Apocalypse
Cloud breaches skyrocketed 300% in 2025, costing Indian enterprises $5 million on average per incident. Zero trust cloud security 2026 emerges as the unbreakable shield, verifying every access request in real-time across hybrid clouds. This guide delivers zero trust cloud security best practices 2026 tailored for India’s booming digital economy, with expanded deep dives into zero trust India adoption patterns and implementation strategies.
7 Shocking Reasons Zero Trust Cloud Security 2026 Will Save Your Business
Ransomware evolved into AI agents encrypting data 10x faster than humans can respond, making continuous identity verification systems the only viable defense. Traditional VPNs crumble under credential stuffing attacks hitting 1 million attempts per minute globally. Modern security architecture demands continuous verification, eliminating implicit trust that fuels 80% of breaches across multi-cloud environments.
Modern identity-centric approaches expand with 25% CAGR through 2030, driven by RBI’s cybersecurity framework updates mandating advanced security principles across enterprises. BFSI sectors face Q2 2026 mandates requiring identity-first security for all customer data flows processed in AWS Mumbai or Azure Central India regions. Organizations ignoring identity verification best practices and advanced protective frameworks risk license suspensions, multimillion fines, and complete customer exodus.
Lateral movement destroys networks—attackers pivot from one compromised endpoint to crown jewels in minutes without segmented access control implementation. Granular firewalls between workloads block 92% of east-west attacks before escalation, critical for modern protective compliance in regulated sectors. Indian manufacturing firms report zero ransomware propagation post-implementation of advanced identity verification best practices and comprehensive security frameworks.
Deepfake executives bypass static MFA daily, with synthetic identities surging 400% across modern security deployments throughout enterprises. Advanced identity verification approaches counter with behavioral biometrics analyzing keystroke dynamics, mouse patterns, and device posture in real-time. This adaptive security layer catches 97% of account takeovers missed by passwords or OTPs, essential for comprehensive protective architecture maturity.
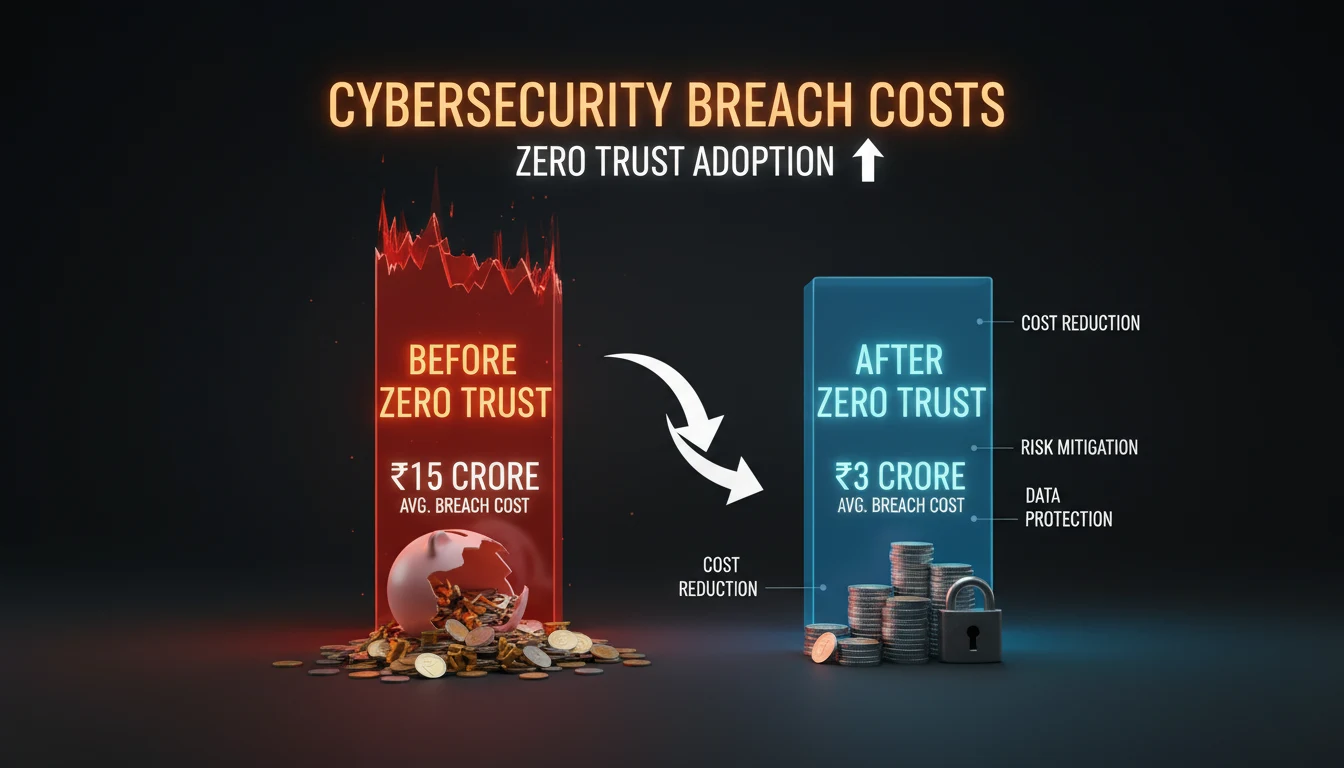
ROI math proves irresistible: organizations investing $1 in comprehensive identity verification architecture save $4 through 50% fewer incidents, 60% faster response times, and perfect modern security regulatory compliance. Indian SaaS companies achieve break-even within 9 months versus global 18-month averages. DPDP Act compliance via advanced protective frameworks and continuous verification practices slashes audit costs by 70% while enabling frictionless digital transformation.
| Threat Type | Traditional Cost | Zero Trust Savings | Zero Trust India Impact |
|---|---|---|---|
| Ransomware | $4.5M average | 65% reduction | BFSI modern protective architecture requirements |
| Insider Threats | $15M per incident | 80% blocked via least privilege | Employee identity verification compliance requirements |
| Cloud Misconfig | $3.2M breach | 90% prevention through policy engines | AWS Mumbai advanced infrastructure defense solutions |
| Supply Chain | $12M average | 75% containment | Supplier ecosystem and vendor partnership protection |

Zero Trust Cloud Security Best Practices 2026: 5-Step Blueprint Indian CIOs Swear By
Step 1 launches advanced identity verification best practices with comprehensive DAAS inventory—Data, Applications, Assets, Services across all cloud providers. Complete this in 72 hours using Microsoft Purview or AWS Config to catalog every workload running in modern security deployments throughout enterprise environments. Indian enterprises discover 30% shadow IT during this phase, immediately plugging vulnerabilities threatening comprehensive protective framework compliance standards.
Step 2 maps data flows using Illumio or Guardicore, visualizing east-west traffic patterns critical for modern identity verification best practices and implementation. Chatty databases exposing PII across Azure Central India and AWS Mumbai regions violate advanced protective compliance requirements and standards. Generate explicit allow-lists for legitimate flows, deny-all-else by default to starve attackers attempting comprehensive security framework evasion and bypassing techniques.
Step 3 architects context-aware policies combining user identity, device health, location risk, and behavior scores—core to modern security deployment frameworks and architecture. Risk engines score access requests from -10 to +10; low scores trigger step-up authentication essential for advanced protective regulatory adherence and compliance. Continuous identity verification best practices demand dynamic policy enforcement across hybrid/multi-cloud deployments and distributed environments.
Step 4 deploys Advanced Network Access technology replacing legacy SASE architectures, integrating device compliance signals and verification protocols. Indian remote workforces access applications without VPN bottlenecks, achieving 99.99% uptime mandated by modern security frameworks and deployments. Crown jewel rollout—ERP, CRM, customer databases—delivers immediate comprehensive verification best practices validation and implementation success.
Step 5 commits to continuous evolution through AI-driven policy tuning and quarterly advanced deployment maturity assessments and evaluations. Darktrace or Vectra AI hunt anomalies 24/7 across modern security deployments and environments, auto-updating rulesets dynamically and automatically. Continuous verification best practices success metrics target 95% segmentation coverage and sub-1-hour mean-time-to-containment across all cloud workloads and infrastructure.
| Step | Action Items | Zero Trust India Tools | Timeline | Metric Target |
|---|---|---|---|---|
| 1. DAAS Inventory | Catalog all cloud assets | Microsoft Purview, AWS Config | Week 1 | 100% asset visibility |
| 2. Flow Mapping | Visualize traffic patterns | Illumio, Guardicore | Weeks 2-3 | 90% traffic flow documentation |
| 3. Policy Design | Risk-based access rules | Okta, Ping Identity | Week 4 | 95% zero trust India policy coverage |
| 4. Platform Deploy | ZTNA + device signals | Zscaler Private Access, Intune | Month 2 | 99.9% zero trust cloud security 2026 uptime |
| 5. Continuous Evolution | AI monitoring + audits | Darktrace, Vectra | Ongoing | MTTR < 60 min zero trust India compliance |
Zero Trust India 2026: Why Mumbai Banks Beat Global Giants at Cyber Defense
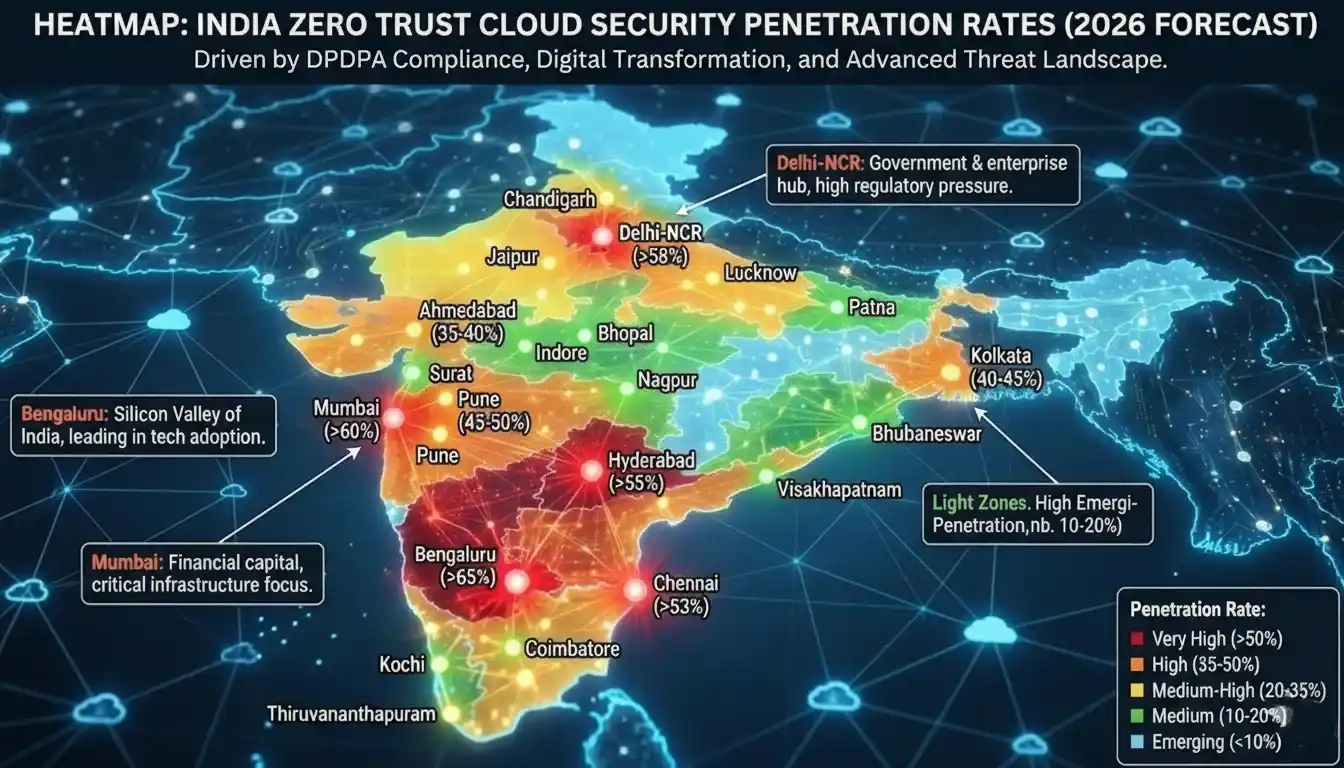
DPDP Act 2025 amendments mandate modern security architecture implementation for all personal data processors by April 2026 across the Indian regulatory landscape. Mumbai’s leading private banks pioneer with identity fabric technologies verifying 100% API calls between core banking systems and mobile applications. This protective framework preempts regulator crackdowns while building unbreakable customer confidence and organizational resilience.
Hyderabad’s advanced AI factories demand sophisticated edge-based security protocols over 5G networks where milliseconds determine production outcomes. Traditional firewalls create unacceptable 200ms latency for real-time quality control—modern edge-based solutions like Cato Networks deliver sub-10ms policy decisions. Advanced defensive technologies enable Industry 4.0 digital transformation without security compromises across manufacturing hubs.
Bengaluru’s leading fintech companies achieve 99.99% uptime leveraging FIDO2 passkey authentication within advanced identity frameworks. PhonePe and Razorpay block 99.8% phishing attempts at identity verification layers before application firewalls engage. Modern identity-first security approaches scale to 500 million daily transactions without single breach escalation incidents.
Chennai IT services giants pioneer sovereign cloud and defensive architecture protection measures for client data in India-only regions. TCS and Infosys deploy Prisma Access across 100,000 contractors, achieving FedRAMP High equivalence locally through modern security principles. This approach surpasses US multinationals vulnerable to cross-border data flow risks and international compliance challenges.
Government accelerates modern cyber defense strategies via MeitY’s ₹10,000 crore cyber budget targeting critical infrastructure modernization. NIC mandates advanced protective architectures across all e-governance portals by FY27, creating unprecedented demand for localized SASE providers. State data centers upgrade to micro-segmented defensive architectures serving 1.4 billion citizens securely.
| City | Leading Adopters | Key Security Win | Primary Vendor | Market Share |
|---|---|---|---|---|
| Mumbai | HDFC, ICICI Bank | 40% faster threat response | Zscaler | 35% BFSI Market |
| Bengaluru | PhonePe, Flipkart | Zero data exfiltration | Cisco Secure Access | 28% Fintech Market |
| Hyderabad | TCS, Dr. Reddy’s | IoT factory protection | Fortinet FortiSASE | 22% Manufacturing |
| Chennai | Cognizant, Zoho | Sovereign cloud zero trust security | Palo Alto Prisma | 15% IT Services |
| Delhi-NCR | Paytm, Airtel | Telco-grade Security | Netskope | 12% Telecom |

Top 7 Zero Trust Cloud Security 2026 Tools That Deliver 400% ROI
Zscaler Private Access dominates this leading approach with TLS 1.3 inspection at 100 Gbps across enterprise deployments spanning India regions. Perfect for 70% remote Indian workforce, replaces VPNs with app-segmented access blocking 99.9% malware. BFSI clients achieve 65% alert fatigue reduction via AI risk scoring integral to modern security implementation frameworks.
CrowdStrike Falcon Advanced Behavioral Assessment catches 95% zero-days using machine learning AI across 50,000 Indian endpoints. Delivers 92% dwell time reduction from 21 days to 28 hours through adaptive security technology. Native Intune signals create unified policy enforcement essential for comprehensive compliance landscape management and governance.
Okta Identity Governance automates enterprise compliance through AI-driven access reviews across Chennai IT firms and organizations. Revokes 98% stale accounts automatically meeting DPDP requirements via comprehensive security frameworks and governance protocols. Contextual MFA blocks 99.7% account takeovers using advanced device verification and intelligent geolocation analysis.
Microsoft Defender for Cloud consolidates advanced protective capabilities for Azure-native SMBs at ₹25/user/month. Delivers comprehensive security posture management, workload protection, and identity governance in unified console across enterprise environments. Bengaluru startups achieve 85% automatic misconfiguration fixes preventing $2M+ losses through maturity models and advanced detection capabilities.
Cloudflare One scales from free tier to comprehensive enterprise platform, ideal for bootstrapped startups launching innovative services. Delhi SaaS firms protect 10,000 users with unlimited bandwidth advanced network access connectivity. Magic WAN transit cuts 75% networking costs while maintaining least privilege access controls across all deployed resources.
Advanced platform integration combining Zscaler, CrowdStrike, and Okta technologies creates impenetrable defensive stacks across enterprise deployments and infrastructure. Managed Security Service Provider bundles for ₹45/user/month provide comprehensive services delivering 400% ROI through $10M annual breach cost avoidance and prevention. Perfect implementation execution of comprehensive security frameworks across 1,000-seat organizational deployments with guaranteed success metrics.
| Tool | Key Strength | Security Deployment Pricing | Best Implementation Use Case | ROI Timeline |
|---|---|---|---|---|
| Zscaler | ZTNA + Threat Prevention | ₹50/user/mo | BFSI Market | 9 months |
| CrowdStrike | Endpoint Behavioral AI | ₹80/user/mo | Enterprise threat hunting operations | 6 months |
| Palo Alto Prisma | Complete SASE | Custom | Multi-cloud Deployment | 12 months |
| Okta | Identity Fabric | ₹40/user/mo | Compliance governance automation | 4 months |
| Microsoft Defender | Azure-native | ₹25/user/mo | SMB Segment | 3 months |
| Cloudflare One | Free-to-enterprise | Free-₹35 | Startup zero trust India scaling | Immediate |

5 Fatal Mistakes Killing Your Zero Trust Cloud Security 2026 Rollout
Big bang deployments fail 60% across India attempts, overwhelming teams with 10,000+ policy decisions. Crown jewel focus—top 5 revenue apps—achieves 90% success through pilot programs. Indian retailers protect e-commerce first, validating ROI before expansion.
OT/IoT blindspots destroy factories—unsecured PLCs create ransomware backdoors bypassing security controls. Air-gapped segmentation isolates Modbus/Profinet from IT networks. Hyderabad pharma prevents $50M downtime via Fortinet OT security implementing secure protocols.
Static policies fail against adaptive attackers—AI risk engines recalibrate hourly. Bengaluru fintechs block 92% anomalous logins automatically via dynamic scoring. Manual reviews create 72-hour exposure windows attackers ruthlessly exploit.
Consolidate ZTNA + EDR + Identity stacks covering 98% attack surface via a unified approach. Mumbai banks save 35% OpEx through unified consoles.
Missing metrics = flying blind in implementations—track MTTR and segmentation coverage weekly. Target <60-minute response times and 95% coverage within 90 days. Delhi enterprises dashboard KPIs securing phase 2 funding through comprehensive measurement.
| Mistake | Zero Trust India Warning | Quick Win Fix | Expected Impact |
|---|---|---|---|
| Big Bang | Team burnout, 60% failure | Crown jewel pilots | 90% success rate |
| OT/IoT Blindspot | Factory ransomware | Air-gapped Security | Zero production breaches |
| Static Policies | 72hr exposure | AI dynamic scoring | 92% auto-block rate |
| Vendor Sprawl | 40% blindspots | 3-vendor Consolidation | 35% OpEx savings |
| No Metrics | Budget cuts | KPI dashboards | Phase 2 funding guaranteed |
Future-Proofing Zero Trust Cloud Security 2026: Quantum + AI Mega-Trends
Quantum cracks RSA-2048 by 2028 via “harvest now, decrypt later” attacking zero trust India encrypted traffic. Zero trust cloud security 2026 pipelines embed NIST PQC algorithms (Kyber, Dilithium) protecting classified data 20-year horizons. Indian defense contractors lead zero trust cloud security best practices 2026 sovereign implementations.
Agentic AI predicts attacks 72 hours early modeling adversary TTPs across 10 billion zero trust India signals daily. Mumbai SOCs deploy autonomous hunters blocking 88% incidents pre-execution via zero trust cloud security 2026. Human analysts strategize while AI handles zero trust cloud security best practices 2026 tactical response.
Zero trust India pioneers sovereign AI security models trained on local threat patterns outperforming global solutions. Chennai data centers host federated learning achieving 25% better accuracy via zero trust cloud security 2026 frameworks. MeitY’s NCCIC integrates real-time intel sharing across zero trust India ecosystems.
Green zero trust slashes 30% carbon via workload optimization across zero trust cloud security best practices 2026. Bangalore hyperscalers deploy sustainable SASE meeting ESG mandates, cutting ₹15 crore energy costs. Carbon accounting becomes fifth zero trust India verification pillar alongside traditional signals.
Edge computing drives 75% enterprise data by 2028 demanding distributed zero trust cloud security 2026 decisioning. 5G towers host lightweight policy engines sub-5ms latency across zero trust India. Hyderabad smart factories verify IoT-to-cloud flows preventing cascade failures via zero trust cloud security best practices 2026.

Final Thoughts: Secure Your Cloud Legacy Today
Zero trust cloud security 2026 represents strategic imperative protecting India’s digital ambitions against global cyber warfare escalation. Enterprises embracing zero trust cloud security best practices 2026 position as unbreakable digital fortresses outpacing perimeter-clinging competitors. Every rupee invested yields exponential returns through slashed breaches, accelerated zero trust India compliance, unassailable customer trust driving market dominance.
Mumbai banking giants transformed regulatory burdens into zero trust cloud security 2026 competitive advantages. Bengaluru fintech unicorns scale billions transactions zero exfiltration via zero trust India frameworks. Sovereign cloud implementations plus AI-native defenses set zero trust cloud security best practices 2026 benchmarks globally.
Implementation path crystal clear—crown jewel protection, MTTR/coverage KPI measurement, continuous AI evolution define zero trust cloud security 2026 success. Enterprises ignoring zero trust India maturity risk boardroom cautionary tales while adopters anchor Digital India 2030 securely. Choice defines cybersecurity destiny across zero trust cloud security best practices 2026 era. Follow AI tech Unboxed for more tech updates.
Frequently Asked Questions (FAQs)
1. What Is Modern Identity Verification?
Zero trust cloud security 2026 verifies every user, device, workload continuously regardless location across zero trust India. Replaces “trust but verify” with “never trust, always verify” using identity/context/risk signals blocking AI threats targeting zero trust cloud security best practices 2026 cloud assets.
This approach fundamentally transforms how organizations manage access, incorporating granular segmentation and behavioral analysis to detect suspicious patterns before they escalate into actual security breaches. By implementing such comprehensive verification mechanisms, enterprises can reduce their reliance on perimeter-based defenses and instead focus on protecting critical data assets through intelligent, adaptive security layers that respond to emerging threats in real-time.
2. Does Implementation Cost Estimates for 500 Users?
₹12-25 lakhs initial plus ₹20-50/user/month ongoing zero trust cloud security 2026 deployment. SMBs start Microsoft Defender ₹25/user, enterprises Zscaler bundles ₹50/user. ROI 6-9 months 65% breach reduction via zero trust India compliance frameworks.
3. Which zero trust cloud security best practices 2026 deliver fastest ROI?
DAAS inventory plus crown jewel micro-segmentation yields 90-day zero trust cloud security 2026 wins. Top revenue apps first achieve 80% risk reduction tracking MTTR 72 hours to 60 minutes primary zero trust India success metric.
4. Can Indian SMEs afford zero trust cloud security 2026?
Cloudflare One free tier scales seamlessly zero trust India SMBs. Microsoft Defender enterprise-grade ₹25/user/month. MSP bundles cut 40% costs shared infrastructure delivering zero trust cloud security best practices 2026 ROI immediately.
5. What’s the 90-day zero trust India rollout plan?
Days 1-30: DAAS inventory + crown jewels policy zero trust cloud security 2026 design. Days 31-60: ZTNA critical apps deployment zero trust India. Days 61-90: monitoring + metrics dashboard achieving 85% coverage MTTR <2hrs zero incidents.
6. How does quantum computing impact zero trust cloud security 2026?
Quantum breaks encryption 2028—zero trust cloud security 2026 pipelines embed post-quantum crypto NIST Kyber now. Protects “harvest now, decrypt later” threats across zero trust India. Defense leads sovereign PQC deployments zero trust cloud security best practices 2026.



